Blog
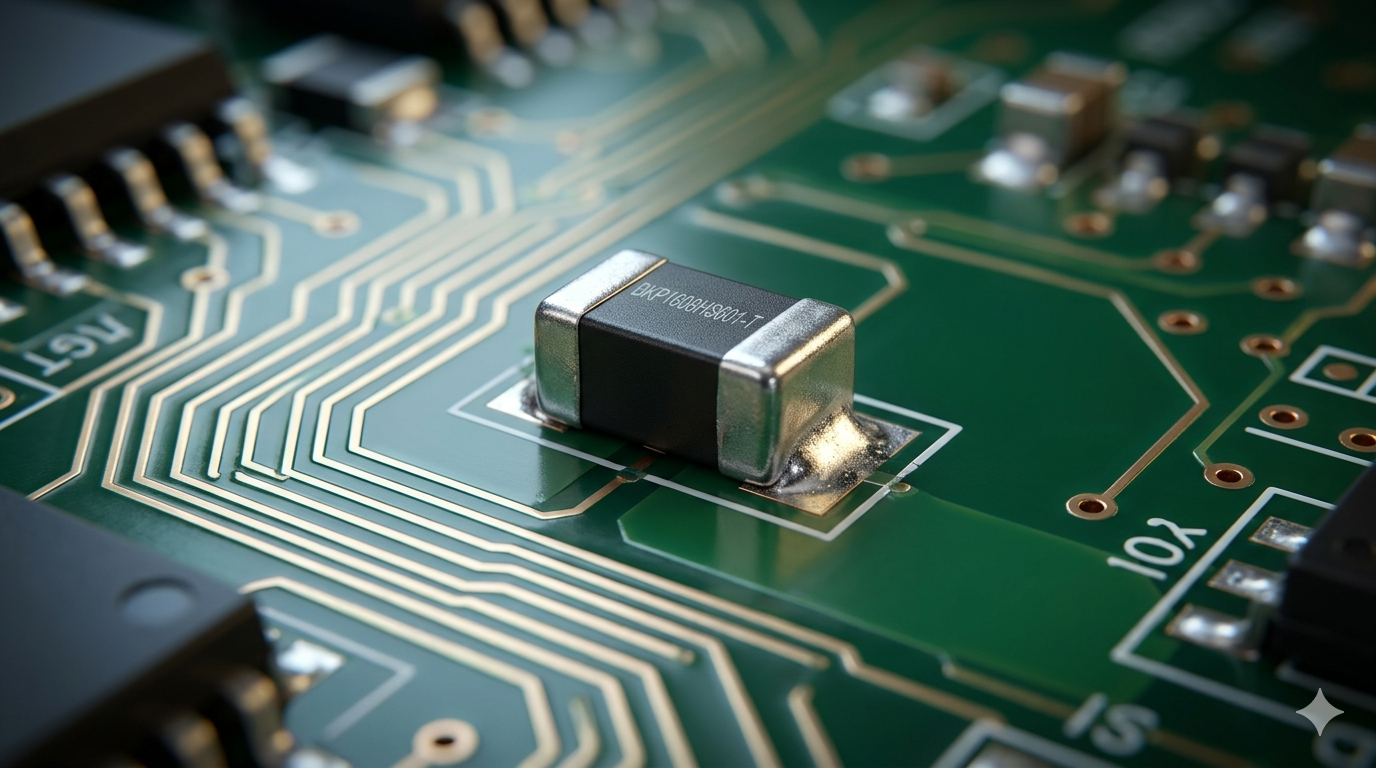
The Ultimate Guide to the bkp1608hs601-t: Taiyo Yuden’s Powerhouse Ferrite Bead
If you have ever spent hours in a lab chasing a ghost in your printed circuit board (PCB) design—perhaps a random voltage spike causing a microcontroller to reset, or a high-frequency switching noise turning your audio output into static—you already understand the absolute necessity of robust electromagnetic interference (EMI) suppression.
When hardware engineers need to filter out aggressive, high-frequency noise on power lines without choking the direct current (DC) power supply, they frequently turn to a specific class of surface mount devices. Enter the bkp1608hs601-t, an industry-standard multilayer chip bead inductor manufactured by Taiyo Yuden.
To answer the critical questions right away: What is it? The bkp1608hs601-t is a ferrite bead designed to offer 600 Ohms of impedance at 100 MHz. Who uses it? Electronics engineers, PCB layout designers, and hardware architects. Where does it go? It is typically placed in series with power supply lines or high-speed digital interfaces. Why is it used? To absorb unwanted high-frequency RF energy and dissipate it as trace amounts of heat, ensuring signal integrity and preventing EMI emissions. How is it implemented? Through standard surface-mount technology (SMT) reflow soldering processes, utilizing its highly compact 0603 footprint.
In this comprehensive engineering teardown, we will strip away the manufacturer marketing jargon. We will explore the exact material science behind Taiyo Yuden’s BKP series, decode the specific thermal and electrical characteristics of this component, and show you exactly how to layout your board to maximize its noise-suppression capabilities.
Decoding the Part Number: What Does bkp1608hs601-t Mean?
To the untrained eye, component part numbers look like a random string of alphanumeric characters. However, Taiyo Yuden utilizes a strict, highly descriptive nomenclature system. Breaking down the bkp1608hs601-t reveals its exact physical and electrical DNA.
-
BK: This prefix designates the component as a “Multilayer Chip Bead Inductor” within Taiyo Yuden’s catalog.
-
P: This single letter is crucial. The “P” indicates that this specific bead is optimized for Power Lines. Standard signal-line beads (which lack the P) often cannot handle the higher DC currents required by power rails and will saturate, rendering them useless for noise filtering. The BKP series is engineered with a thicker internal silver-printed layer to handle higher current loads with minimal voltage drops.
-
1608: This denotes the physical dimensions of the component using the metric system. It measures 1.6 mm in length by 0.8 mm in width. In the more commonly used imperial sizing system, this translates exactly to an 0603 package.
-
HS: This refers to the specific ferrite material composition. “HS” stands for High-Speed. In Taiyo Yuden’s material science, HS ferrite materials feature a low R-XL cross-point frequency characteristic. This means it provides a large resistive element that acts as a dampening function, effectively suppressing unnecessary resonance and maintaining sharp signal integrity on high-speed digital lines.
-
601: This is the nominal impedance value code. The first two digits are the base number (60), and the third digit is the multiplier (10^1). Therefore, 60 x 10 = 600 Ohms. By standard convention, this impedance is measured at a test frequency of 100 MHz.
-
-T: The suffix denotes the packaging method for the pick-and-place assembly machines. The “T” stands for standard Taping (Tape and Reel packaging).
Core Electrical Specifications and Technical Data
When evaluating the bkp1608hs601-t for your bill of materials (BOM), the raw specifications dictate whether it will survive your circuit’s operational environment. Here is the critical data profile for this exact component:
-
Nominal Impedance: 600 Ω (± 25% tolerance) at 100 MHz.
-
Maximum DC Resistance (DCR): Usually around 0.15 to 0.20 Ohms for the 600-Ohm HS variant. (Lower DCR is critical in power applications to prevent unwanted voltage drops across the bead).
-
Maximum Rated Current: Typically ranging between 1.0A to 1.5A for the 600-ohm BKP variant, allowing it to sit comfortably on standard 3.3V or 5V logic power rails without saturating the magnetic core.
-
Operating Temperature Range: -55°C to +125°C, making it suitable for harsh industrial environments and enclosed consumer electronics prone to thermal buildup.
-
Compliance: Fully RoHS compliant, Halogen-Free, and REACH SVHC compliant.
Understanding the Impedance Curve
You cannot evaluate a ferrite bead solely by its 100 MHz rating. The true value of the bkp1608hs601-t lies in its frequency response curve. A ferrite bead acts as an inductor at low frequencies (reactance) and as a resistor at high frequencies.
The “HS” material formulation ensures that the transition point—where the bead stops reflecting noise and starts actively absorbing and dissipating it as heat—occurs at the optimal frequency to counter high-speed digital harmonic noise. If you are dealing with ringing on a clock line or switching noise from a DC-DC buck converter operating in the megahertz range, the 600-ohm impedance presents a massive roadblock to those parasitic frequencies, cleaning up the power rail before it reaches sensitive ICs.
Why Hardware Engineers Choose the BKP Series for EMI Suppression
Designing a modern PCB is an exercise in managing chaos. As processors get faster and board real estate shrinks, digital logic lines sit uncomfortably close to analog sensors and radio frequency (RF) antennas.
The Saturation Problem
A common mistake junior engineers make is grabbing any generic 0603 ferrite bead with the correct impedance and dropping it onto a power rail. They boot the board, apply a load, and suddenly the EMI noise returns. Why? Because of DC bias saturation.
When direct current flows through a ferrite core, it creates a magnetic field. If the current is too high, the core “saturates,” meaning it physically cannot hold any more magnetic flux. Once a bead saturates, its impedance plummets to near zero. It effectively turns into a standard wire, offering zero noise suppression.
The bkp1608hs601-t circumvents this. Because of the “P” (Power) designation, its internal closed magnetic circuit is specifically designed to maintain its impedance curve even when biased with higher DC currents. This makes it an incredibly reliable choice for isolating the power inputs of sensitive phase-locked loops (PLLs), analog-to-digital converters (ADCs), and precision operational amplifiers.
Pro Tip: The Pi-Filter Layout Strategy Never use a ferrite bead in isolation if you can avoid it. To maximize the effectiveness of the bkp1608hs601-t, utilize it as the central element of a “Pi-Filter” (π-filter). Place a low-ESR ceramic decoupling capacitor (like a 0.1µF or 1µF) from the power line to the ground immediately before the bead, and place another capacitor immediately after the bead. This creates an aggressive low-pass filter network that will utterly crush high-frequency power supply ripple. Keep the PCB traces between the bead, the capacitors, and the IC power pins as physically short as possible to minimize parasitic trace inductance.
PCB Layout and Assembly Considerations
Because the bkp1608hs601-t utilizes a 1608 metric (0603 imperial) form factor, it sits in a goldilocks zone for modern manufacturing. It is small enough to allow for high-density board routing, yet large enough that it does not require ultra-premium, high-precision assembly equipment like microscopic 0201 or 01005 components do.
Thermal Relief and Soldering
When designing the copper land patterns (pads) for this component, symmetry is key. Ensure that both pads connected to the bead have relatively equal thermal mass. If one side connects directly to a massive, continuous copper power plane without thermal relief spokes, and the other side connects to a thin 10-mil signal trace, you risk “tombstoning” during the reflow oven process.
Tombstoning occurs when the solder paste on the thin trace melts and wicks faster than the paste on the heavy power plane. The surface tension of the liquid solder physically pulls the bkp1608hs601-t upright, disconnecting one side and ruining the board yield. Always use properly calculated thermal reliefs on solid polygon pours to ensure even heating.
Cross-Reference and Supply Chain Alternatives
In the era of global semiconductor shortages and supply chain volatility, relying on a single manufacturer for a passive component is a risky strategy. While the bkp1608hs601-t is an exceptional part, a senior strategist must always have second-source options ready for the procurement team.
If Taiyo Yuden lead times stretch too far, look for power-line rated, 0603-sized, 600-ohm ferrite beads from competing top-tier manufacturers.
-
Murata: Look into their BLM18P series (e.g., BLM18PG or BLM18KG series). The “18” denotes the 0603 size, and the “P/K” denotes power line suitability.
-
TDK: The MPZ1608 series serves as a direct competitor, offering high-current capabilities in the exact same footprint.
-
Würth Elektronik: The WE-CBF series (specifically the high-current variants in the 0603 package) offers excellent documentation and similar impedance profiles.
Always verify the DC Resistance (DCR) and Maximum Current ratings of any alternative. Matching the 600-ohm impedance is easy; matching the thermal and current-handling capabilities of the BKP series requires careful datasheet scrutiny.
Frequently Asked Questions (FAQ)
What is the difference between the BKP and the standard BK series? The Taiyo Yuden BK series is designed for general signal lines and cannot handle large amounts of direct current before experiencing core saturation. The BKP series features an optimized internal structure designed specifically for power lines, allowing it to maintain high impedance and filter noise even when carrying higher DC loads.
Can I use the bkp1608hs601-t on an I2C or SPI data line? While you physically can, it is generally not recommended to use a power-line (P-series) bead on high-speed data lines unless explicitly required. The 600-ohm impedance and the specific HS material could potentially roll off the sharp rising and falling edges of your digital square waves, leading to timing errors or data corruption. Standard BK series beads are better suited for purely digital signal integrity.
How do I test if the bkp1608hs601-t is working in my circuit? You will need an oscilloscope with a high-bandwidth probe. Measure the AC voltage ripple on the power rail before the ferrite bead, and then measure it again on the pad immediately after the bead. If the component is functioning correctly and correctly matched to the noise frequency, you should observe a massive reduction in high-frequency voltage spikes and ringing on the output side.
Does orientation matter when placing a ferrite bead on a PCB? No. Multilayer chip bead inductors like the bkp1608hs601-t are non-polarized passive components. They can be placed in either direction on the PCB footprint without affecting their electrical performance or EMI suppression capabilities.
Final Thoughts on Component Selection
Selecting the right passive components is often the difference between a prototype that barely passes FCC/CE emission testing and a rock-solid, commercial-grade product. The bkp1608hs601-t is not just a random resistor; it is a highly engineered, frequency-dependent filter that protects the most vulnerable parts of your digital architecture. By understanding its “High Speed” material properties, respecting its current limits, and implementing proper Pi-filter layouts, you guarantee cleaner power, stable IC performance, and a much smoother path to market.
● Live Updates
Online Casino Canada Guide: Best Real Money Sites & Bonuses

The landscape of online gambling has grown rapidly across Canada as more players turn to digital platforms for entertainment and real money gaming. Millions of Canadians now use computers, smartphones, and tablets to play their favorite casino games from anywhere at any time. The Canadian online casino industry provides players with many licensed and regulated options that focus on safe gaming experiences. Provincial gambling laws allow flexibility for players to select from trusted sites that offer large game collections, strong bonus programs, and secure payment methods built for Canadian users.
When searching for the ultimate digital platform, players often use helpful directories like online casino www.850dollarbonus.com to discover high-value promotions and vetted platforms. Understanding which sites are legitimate and how to maximize your bankroll is the secret to a premium safe gaming experience.
Trusted Gaming Sites for Canadian Players
Several casino platforms stand out for their solid track records with Canadian players. Luxury Casino, Zodiac Casino, and Yukon Gold Casino have built strong reputations through consistent service delivery. These sites belong to the Casino Rewards network and offer reliable gaming experiences. Players find their withdrawal systems work smoothly without delays. Support teams answer questions quickly when issues arise.
Notable features of these platforms:
-
Large game collections with well-known titles
-
Clear and honest payment methods
-
Fair gaming practices that players can trust
-
Years of stable operations
The gaming community in Canada gives positive feedback about these brands regularly. Players often mention how dependable these casinos are in their reviews and recommendations to other users.
Is 888 Casino Real? evaluating Brand Legitimacy
When beginners enter the digital arena, the primary question they ask is: Is 888 casino real? The definitive answer is yes. Operating since 1997, this platform is one of the oldest and most respected global giants in the iGaming sector. It holds active credentials from stringent regulators, including the UK Gambling Commission and the Malta Gaming Authority. For local players, it is fully compliant with regional frameworks, providing tailored services across various provinces.
The site utilizes audited Random Number Generators (RNG) to guarantee that every spin of a virtual slot reel or flip of a card is entirely arbitrary. Independent testing bodies like eCOGRA regularly audit their systems to confirm fair payout ratios. This transparency ensures that you are dealing with an authentic enterprise rather than a rigged simulation.
+------------------------+---------------------------------------+
| Feature | 888 Casino Specifications |
+------------------------+---------------------------------------+
| Year Established | 1997 |
| Regulatory Licenses | UKGC, MGA, AGCO (Ontario) |
| Independent Auditor | eCOGRA Certified |
| Minimum Deposit | $10 CAD |
+------------------------+---------------------------------------+
Can I Play Casino Online for Real Money Safely?
The next logical milestone for a player is asking: Can I play casino online for real money? You absolutely can, provided you select an platform that possesses authentic domestic or international credentials. Depositing real Canadian Dollars (CAD) unlocks access to identical prize pools, progressive jackpots, and live croupier tables found inside land-based venues.
To complete this safely, check for secure payment methods like Interac, Instadebit, and major credit cards. These banking options feature advanced encryption layers that insulate your financial statements from third-party intervention. Furthermore, established digital hubs require identity confirmation protocols prior to your initial cashout. While this paperwork might feel tedious, it effectively blocks fraudulent entities and secures your hard-earned winnings.
Casino Rewards Maximum Payout Promise
The Casino Rewards member casinos deliver a unique commitment that distinguishes them from typical online gaming sites. This pledge ensures players access games set to their maximum Return to Player (RTP) percentages straight from software developers.
Primary Elements of This Commitment:
-
Maximum RTP Configuration: All games run at their highest available payout settings.
-
Universal Implementation: Each member casino maintains these enhanced percentages.
-
Player Benefits: Superior RTPs extend playing time and boost winning chances.
While most online casinos choose lower RTP versions to maximize house profits, Casino Rewards brands follow a different strategy. They implement the highest RTP settings throughout their entire game collections. This approach means players get better value from their deposits and enjoy extended gaming sessions with identical bankroll amounts. The promise applies to every game type including slots, table games, and specialty selections.
Key Takeaways
RTP Settings Matter: Always seek out operators that implement the highest possible Return to Player configuration to stretch your entertainment budget.
Verification Guards Capital: Legitimate sites require identity verification, protecting your account from unauthorized withdrawals.
Vetted Lists Save Time: Relying on curated aggregators helps bypass predatory platforms completely.
Which Online Casino Gives a Welcome Bonus?
If you want to maximize your opening transaction, you need to know which online casino gives a welcome bonus that provides genuine equity. Most premium establishments offer a combination of deposit matches and complimentary slot rounds to attract newcomers.
For instance, platforms showcased on aggregators like online casino www.850dollarbonus.com specialize in identifying massive promotional packages. Some brands offer tiered reward structures that span your initial five deposits, boosting your bankroll significantly. However, an expert player always reviews the underlying terms. Look for wagering requirements close to 30x or lower, ensuring you can realistically convert those promotional credits into real cash.
How to Play Casino Games and Win Online for Free
It sounds like a paradox, but figuring out how to play casino games and win online for free is entirely achievable through two primary avenues: demo configurations and no-deposit incentives.
+----------------------------+-------------------------------------------------------------+
| Free Play Method | Core Benefit |
+----------------------------+-------------------------------------------------------------+
| Practice Demo Mode | Zero financial risk; ideal for mastering intricate rules |
| No-Deposit Free Spins | Keep real cash winnings after meeting play-through terms |
+----------------------------+-------------------------------------------------------------+
Virtually every regulated platform permits users to load titles in a practice state. This allows you to explore complex features, understand paylines, and build a cohesive plan without risking a single penny. To actually win tangible capital without an upfront investment, seek out validated no-deposit credits. These specific campaigns grant a small batch of complimentary rounds upon account creation. If you fulfill the clear wagering parameters outlined in the rules, the leftover profits are yours to keep.
Sports and Global Entertainment Connections
The modern gaming community frequently intersects with global sports culture. Enthusiasts who enjoy high-stakes strategy often follow competitive football tournaments globally. For instance, analyzing the strategic architecture of the Saudi Arabia football squad requires an analytical mindset similar to mastering blackjack probabilities.
Securing your position at premier events via the FIFA Visa presale portal mirrors the thrill of catching a time-sensitive live dealer tournament online. For broader updates on major international athletic events and venue schedules, visiting a central resource like FIFA World offers great perspective. Even tracking historical ticket distributions, such as the highly anticipated Mexico vs South Africa tickets exchange, shows how global entertainment systems rely on robust, secure transactional frameworks just like top-tier digital gaming platforms.
Essential Safety Protocols for Canadian Players
Before finalizing your choice, establish a rigorous screening routine to ensure absolute safety:
-
Verify the Footer Info: Legitimate platforms display their active license numbers, regulatory logos, and corporate registration details transparently at the bottom of the homepage.
-
Inspect the URL Security: Ensure the web address starts with “https” and displays a closed padlock icon, verifying that your data transfers are fully encrypted.
-
Evaluate Responsible Gaming Controls: Safe operators offer built-in player tools, including customizable deposit thresholds, loss limits, and self-exclusion periods to help maintain healthy habits.
By sticking to these verified evaluation methods and utilizing trusted tracking indexes, you can easily avoid rogue operators. This ensures your interactive entertainment remains consistently secure, fair, and highly rewarding.
Conclusion
Navigating the Canadian digital gaming space is safe and highly rewarding when you prioritize regulatory compliance and transparent payout structures. Utilizing resources like online casino www.850dollarbonus.com allows you to discover premium bonus packages and vetted platforms with ease. By understanding game mechanics, verifying license credentials, and practicing sound bankroll management, you can confidently enjoy real money entertainment while fully protecting your personal information and financial capital.
Frequently Asked Questions
Is it legal to play at online casinos in Canada?
Yes, online gambling is legal across Canada. Players can legally access provincially regulated platforms as well as licensed offshore websites that securely serve the Canadian market.
What does the Casino Rewards maximum payout promise mean?
This commitment ensures that all member platforms configure their games to the highest native Return to Player (RTP) percentages provided by developers, maximizing your long-term winning chances.
How do I cash out real money winnings from a casino site?
Navigate to the virtual cashier section, select a secure transaction method like Interac or a direct bank transfer, enter your desired withdrawal amount, and submit the request for standard processing.
Can I try out casino titles without spending money?
Absolutely. Most trusted sites offer a dedicated practice or demo setting for their game libraries, allowing you to learn the specific rules and mechanics with zero financial obligation.
What should I check to confirm a gaming platform is safe?
Always verify that the platform displays an active license from a recognized regulator, holds a valid SSL encryption certificate, and features independent fairness certifications from auditing bodies like eCOGRA.
Blog
Deep Dive into Casino Software Architectures and Fairness Features

The global entertainment ecosystem has transitioned aggressively toward cloud-hosted platforms. Across Canada and various global markets, millions of active users rely on their smartphones, computers, and tablets to play interactive, real-money games at any hour. This massive wave of digital adaptation is not just a trend; it represents a major milestone in scalable backend systems and secure database administration. To discover premium tech insights regarding modern tools, explore thesoftwarefeatures.com.
When consumers search for competitive introductory offers or analyze platforms like the online casino www.850dollarbonus.com, they interact primarily with a graphical user interface (UX). However, the long-term value, reliability, and security of any gaming platform are determined entirely by its underlying software features. These core components handle complex calculations, secure financial handshakes, and process continuous data streams without lag.
The Backend Infrastructure of Modern Gambling Software
Building an online casino that can support thousands of concurrent players requires a highly decoupled microservices architecture. Unlike legacy monolithic software frameworks, contemporary iGaming operations isolate key functionalities into independent modules. For example, user profiles, financial ledgers, and the gaming mechanics themselves exist as autonomous services communicating via secured Application Programming Interfaces (APIs).
This structural separation means that if a high-profile bonus campaign causes a sudden traffic spike on a marketing landing page, the critical game engine microservice continues running unaffected.
Furthermore, robust distributed hosting solutions prevent service interruptions. Respected platforms within networks like the Casino Rewards group—including Luxury Casino, Zodiac Casino, and Yukon Gold Casino—depend heavily on these distributed systems. This foundational setup eliminates withdrawal processing friction and guarantees fast payouts for Canadian players. Administering such a highly resilient digital architecture requires sophisticated enterprise management strategies, many of which are outlined in this comprehensive ultimate PC software guide.
Data Encryption and Transaction Security Software
Any application dealing with real-time financial tracking must prioritize cryptographic integrity. Modern casino software layers various security mechanisms to safeguard data packets traveling between the end-user device and the host servers. This includes utilizing advanced Transport Layer Security (TLS) and 256-bit Secure Sockets Layer (SSL) encryption protocols.
In regulated markets, provincial frameworks require casino operators to embed automated fraud-detection engines within their transaction pipelines. These algorithms flag irregular betting patterns, multi-accounting attempts, and potential money laundering activities instantly.
Protecting user identities and transaction logs matches the strict corporate protocols used by the top 10 most used business software solutions across the tech sector today. For a detailed breakdown of global encryption standards, you can review the technical documentation provided by internet security leaders like Cloudflare.
Key Takeaways
Modern casino architectures rely on decentralized microservices to maintain platform stability during high-volume traffic surges.
Certified Random Number Generators (RNGs) provide mathematically verifiable game outcomes that cannot be manipulated by operators or users.
Strict automated geo-fencing frameworks allow platforms to remain compliant with regional, provincial, and national legal boundaries automatically.
The Software Logic of Micro-Games: A Focus on Plinko
A significant portion of modern gaming software innovation centers around interactive arcade-style gambling. Instead of conventional spinning reels, titles like Plinko leverage real-time physics engines alongside randomized numerical inputs to simulate falling chips on a peg board.
Because of this shifting preference, many users look for platforms hosting these specific titles. When analyzing Which online casino has Plinko?, developers emphasize choosing brands that source their games from verified, externally audited software providers rather than unverified third parties.
Major operators regularly adjust their available libraries to reflect current player demand. For instance, players routinely ask, Does 888 casino have Plinko? to verify if that specific brand has licensed the game script from creators like Spribe or BGaming. Integrating these dynamic modules requires smooth API hooks to sync the game’s graphical physics calculation directly with the casino’s secure database layer.
Users unfamiliar with these digital mechanics often have foundational questions about how these systems pay out, such as, Is Plinko earn real money? In short, yes—the software treats it as a legitimate gambling module where real capital is risked for real financial returns.
However, players must understand the integrated mathematical constraints. When investigating What are the risks of playing Plinko?, the most critical hazard is the immutable house edge programmed directly into the software’s algorithm. The chip’s path looks completely organic, but the distribution probabilities ensure the platform maintains a consistent mathematical advantage over a prolonged number of rounds.
Mobile Application Architectures and User Experience (UX)
Because a majority of web traffic originates from mobile hardware, casino engineers focus deeply on cross-device functionality. When trying to determine What are the best casino apps to win real money?, the ultimate answer depends on execution quality—specifically, asset compression, memory optimization, and low battery drain.
Developers utilize Progressive Web Apps (PWAs) or native language apps (such as Swift for iOS and Kotlin for Android) to provide fluid touch response and immediate loading sequences. These mobile applications use localized caching mechanics to keep real-time odds and account balances synchronized, even if a user encounters a fluctuating cellular signal.
Keeping track of your digital expenditures across various apps requires dedicated budgeting solutions, similar to managing personal finances with tools like Quicken Simplifi.
Compliance, Geo-Fencing, and International Restrictions
Software systems must also dynamically adapt to complex global legal frameworks. Online gaming systems deploy sophisticated IP filtering and automated geo-fencing software to evaluate a visitor’s exact physical coordinates before allowing them to create an account or place a bet.
This automated tracking becomes highly relevant when evaluating specific regional regulatory boundaries. For example, a common inquiry is, Is Plinko legal in Pakistan? In that specific country, federal laws strictly prohibit almost all forms of computerized real-money gambling.
Consequently, compliant casino software recognizes incoming Pakistani IP connections and automatically blocks access to safeguard the user and ensure corporate adherence to local laws. For further information on player safety standards and regulatory compliance worldwide, consult the official guidelines published by the Kahnawake Gaming Commission.
Conclusion
The digital casino industry depends heavily on sophisticated software features to maintain user trust, security, and game fairness. From microservices architecture to certified random number generators, the backend technology dictates the quality of the player experience. While attractive bonuses can draw users to a platform, long-term success relies entirely on technical stability, data encryption, and transparent operations. Prioritizing platforms with verified infrastructure ensures a highly safe and enjoyable digital environment.
Frequently Asked Questions (FAQ)
1. How do casino software providers prove their games are fair?
Reputable software studios submit their core game source code and Random Number Generator (RNG) engines to independent third-party labs like eCOGRA or iTech Labs. These firms run millions of simulated rounds to verify that game outcomes are completely random and match the advertised return-to-player (RTP) percentages.
2. Can geo-fencing software block me from accessing a casino app?
Yes. If you travel into a state, province, or country where online real-money gambling is legally restricted, the application’s embedded geo-fencing algorithms will pinpoint your GPS or IP data and temporarily lock your gaming capabilities to stay compliant with local regulations.
3. What makes a casino application technically stable?
Technical stability relies on using a microservices architecture. By splitting player authentication, live chat support, payments, and game loading into separate server containers, the core gaming software remains stable even if one specific feature experiences an outage or a massive traffic surge.
4. Why do platforms use API integrations for games like Plinko?
Instead of developing every title from scratch, casinos use secure API integrations to display games hosted directly on the secure servers of certified software studios. This ensures that the game logic cannot be modified or tampered with by the casino operator.
5. What security standard should I check for before depositing?
Before submitting any financial information, ensure the website address begins with “https://” and displays a padlock icon in your browser address bar. This confirms that active TLS/SSL encryption software is shielding your data transfers from external interceptors.
Blog
Is ASMR Getting Too Real? The Truth Behind Sleepy Sab’s ‘Little Game’
The world of ASMR has changed. We’ve moved way beyond simple glass-tapping. Now, it’s all about complex, high-production roleplays. At the center of this is Sleepy Sab. She’s mastered “gamified ASMR,” and her “Let’s play a little game” concept is currently blowing up on social media and Fansly.
If you’ve seen the trending searches about “leaks,” you’re seeing a collision of content creation, privacy, and the new economics of the creator-fan relationship. Let’s break down what’s actually happening and why it matters.
The Psychology of the “Game”
Why does a “game” hook work so well for relaxation? Traditional ASMR is passive. You just listen. But Sleepy Sab uses cognitive engagement. By framing a video as a game, she grabs your full attention. It sounds counterintuitive for sleep, but it actually mimics meditation. When she tells you to “look here” or “pick a card,” your brain focuses on one task, which kills the background noise of daily anxiety.
Common Triggers
- Visual Tracking: Moving objects to help your eyes and brain relax.
- Decision-Based Triggers: Asking you to pick a color or side for a personalized feel.
- Close-up Whispering: Using high-end mics to make it feel like she’s standing right next to you.
The Fansly Move: Why Paywalls?
For years, creators relied on YouTube ads. But strict rules on “suggestive” content—even if it’s purely therapeutic—forced a move. Fansly gives creators like Sab more freedom. They can offer tiered access, experiment with “spicier” content, and get direct support from fans to afford $1,000+ microphones. The “leak” culture around these platforms is a double-edged sword. It shows high demand, but it also hurts the creator’s ability to keep making great stuff.
The “Leak” Reality Check
When you search for “leaks,” you usually end up on “scraper” sites. These are rarely safe. Most sites claiming to have leaked content are full of malware and phishing scams. They want you to click a link or download a “player” that compromises your security. Plus, ASMR is personal. When content is stolen, it violates the safe space these artists try to create.
Pro Tip: Always check a creator’s official Linktree. If a site isn’t linked there, it’s a scam. Support artists directly to keep your data safe and the content coming.
Final Thoughts
Sleepy Sab’s “Let’s play a little game” is a masterclass in interactive storytelling. While the temptation for free content is high, the risks to your digital health and the creator’s livelihood are real. Respect the craft, support the source, and enjoy the tingles safely.
-

 Business3 months ago
Business3 months agoUnderstanding Halifax for Intermediaries: A Comprehensive Guide
-

 Entertainment3 months ago
Entertainment3 months agoThe Ultimate Upcoming Netflix Movies 2026 List: Every Major Release Coming to Your Screen
-

 Entertainments3 months ago
Entertainments3 months agoTop 10 Most Anticipated Movierulz Kannada Movie of 2025-26
-
 Blog3 months ago
Blog3 months agoN&S Locating Services Layoffs: What Happened and What’s Next
-

 Business3 months ago
Business3 months agoThe Best Kickstand for Your Giordano C700 Women’s Bike
-

 Technology6 months ago
Technology6 months agoWUSVCS Explained | What It Is and How It Works in Windows
-

 ● Live Updates4 months ago
● Live Updates4 months agoUnderstanding the CaraSolva Login Process and Platform Benefits
-

 Uncategorized3 months ago
Uncategorized3 months agoUnderstanding 小火箭 Little Rocket VPN 5.1.3: The Ultimate Proxy Client





















